Ransomware Resiliency For Storage & Backup: Trends, Threats & Tips
One thing is clear. The “business value” of data continues to grow
- |
- Written by Doron Pinhas, CTO at Continuity

It’s all about the data
One thing is clear. The “business value” of data continues to grow, making it a bank’s primary piece of intellectual property.
From a cyber risk perspective, attacks on data are the most prominent threat to banks.
Regulators, cyber insurance firms, and auditors are paying much closer attention to the integrity, resilience, and recoverability of bank’s data — as well as the IT infrastructure & systems that store the data.
So, what does this mean for the security of enterprise storage & backup systems?
Just a few years ago, almost no banking CISO thought that storage & backups were important. That’s no longer the case today.
Ransomware has pushed backup and recovery back onto the IT and corporate agenda.
Ransomware groups such as Conti, Hive and REvil are actively targeting enterprise storage and backup systems, to prevent banks from recovering their data.
Here are some of the headlines from those attacks:
https://www.continuitysoftware.com/resources/?resources_category=headlines
These attackers realize that an attack on storage or backup systems is the single biggest determining factor to show if the bank will pay the ransom.
This has forced banks to look again at potential holes in their safety nets, by reviewing their storage, backup and data recovery strategies.
Analysis of Storage & Backup Security in the Banking & Financial Services Sector
We published a research report at the end of last year, where we surveyed 200 infosec leaders within the banking and financial services sector. One of the most alarming findings was…
Almost 60% of respondents are not confident in their ability to recover from a ransomware attack.
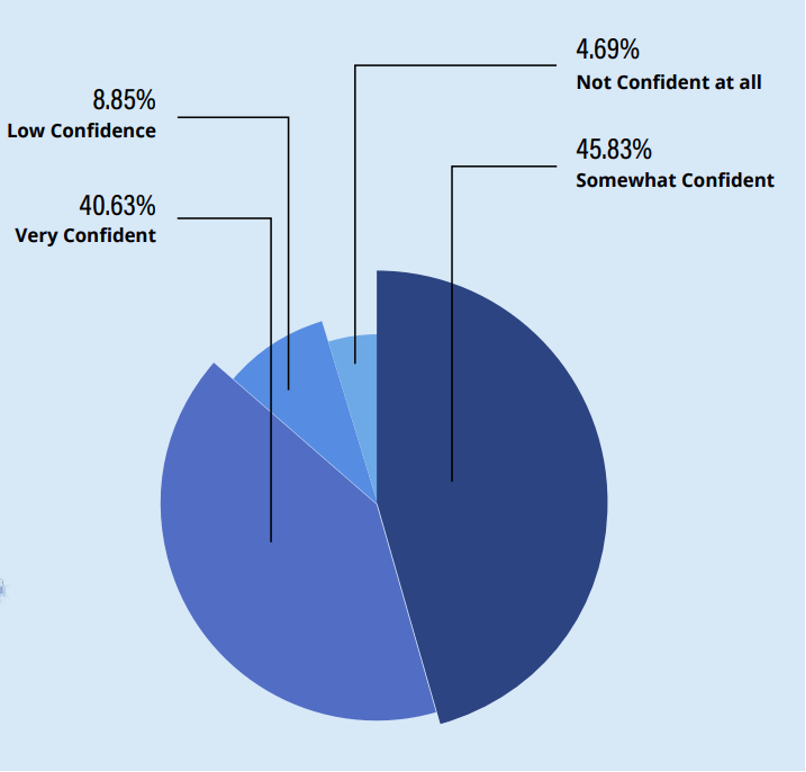
Source: Continuity; Financial Services Security Intelligence Report
There’s clearly a recognition that as an industry, we have security blind spots.
Without a sound storage, backup and recovery strategy, companies have little chance of surviving a ransomware attack, even if they do end up paying the ransom.
The banking sector is one of the most heavily regulated industries. Audits are performed both internally and externally and tend to evolve year-over-year based on advances in technology, industry regulation changes, and shifts in the threat landscape.
It was interesting to learn how pervasive storage and backup security controls have become, as part of IT auditing. In fact, more than two-thirds of respondents identified securing storage and backup being specifically addressed in recent external audits.
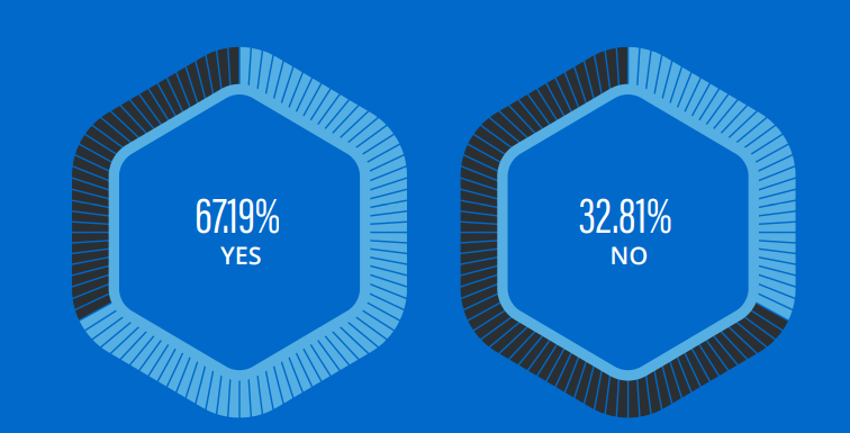
Source: Continuity; Financial Services Security Intelligence Report
Summary & Recommendations
Considering storage and backup compromise are at the heart of all current ransomware kits, surely the time has come for us to boost our knowledge — as well as our strategies — in protecting and hardening our storage and backup systems.
While immutability is helpful in remediating cyberthreats, it is only the beginning of a comprehensive cyber resiliency strategy.
According to the analyst firm, Gartner:
“Harden the components of enterprise backup and recovery infrastructure against attacks by routinely examining backup application, storage and network access and comparing this against expected or baseline activity.”
You wouldn’t dream of not continuously scanning your endpoints, OS and network layers for security risks. So why wouldn’t you do it for your most important layer of IT?
This is why I recommend deploying a vulnerability management solution to help you continuously scan your storage & backup systems, to automatically detect security misconfigurations and vulnerabilities.
These solutions also prioritize risks in order of urgency and business impact, and some of them even include remediation guidance and auto-remediation features.
The 5 key opportunities for improvement include:
- Assign higher priority to improving the security of enterprise storage and backup systems
- Build up knowledge and skill sets – and improve collaboration between your Infosec and IT infrastructure teams
- Define comprehensive security baselines for all components of storage and backup systems
- Use automation to reduce exposure to risk, and allow much more agility in adapting to changing priorities. Vulnerability management solutions can go a long way to helping you reduce this exposure.
- Apply much stricter controls and more comprehensive testing of storage security and the ability to recover from an attack. This will not only improve confidence, but will also help identify key data assets that might not meet the required level of data protection
Author: Doron Pinhas, Chief Technology Officer, Continuity. Doron is an avid Storage and Backup security advocate, and one of the two authors of the recently published NIST special publication titled: “Security Guidelines for Storage Infrastructure”.
Related items
- Banking Exchange Hosts Expert on Lending Regulatory Compliance
- Merger & Acquisition Round Up: MidFirst Bank, Provident
- FinCEN Underestimates Time Required to File Suspicious Activity Report
- Retirement Planning Creates Discord Among Couples
- Wall Street Looks at Big Bank Earnings, but Regional Banks Tell the Story













